What We Deliver
Siege Cyber provides end-to-end SOC 2 readiness and audit preparation for Australian companies. We work with your team to design, implement, and document the controls required to pass a SOC 2 audit, whether you are pursuing Type 1 (point-in-time) or Type 2 (over a period of time). Then we prepare you for the formal audit, help you manage the observation period, and support you through report issuance.
Here is what you get:
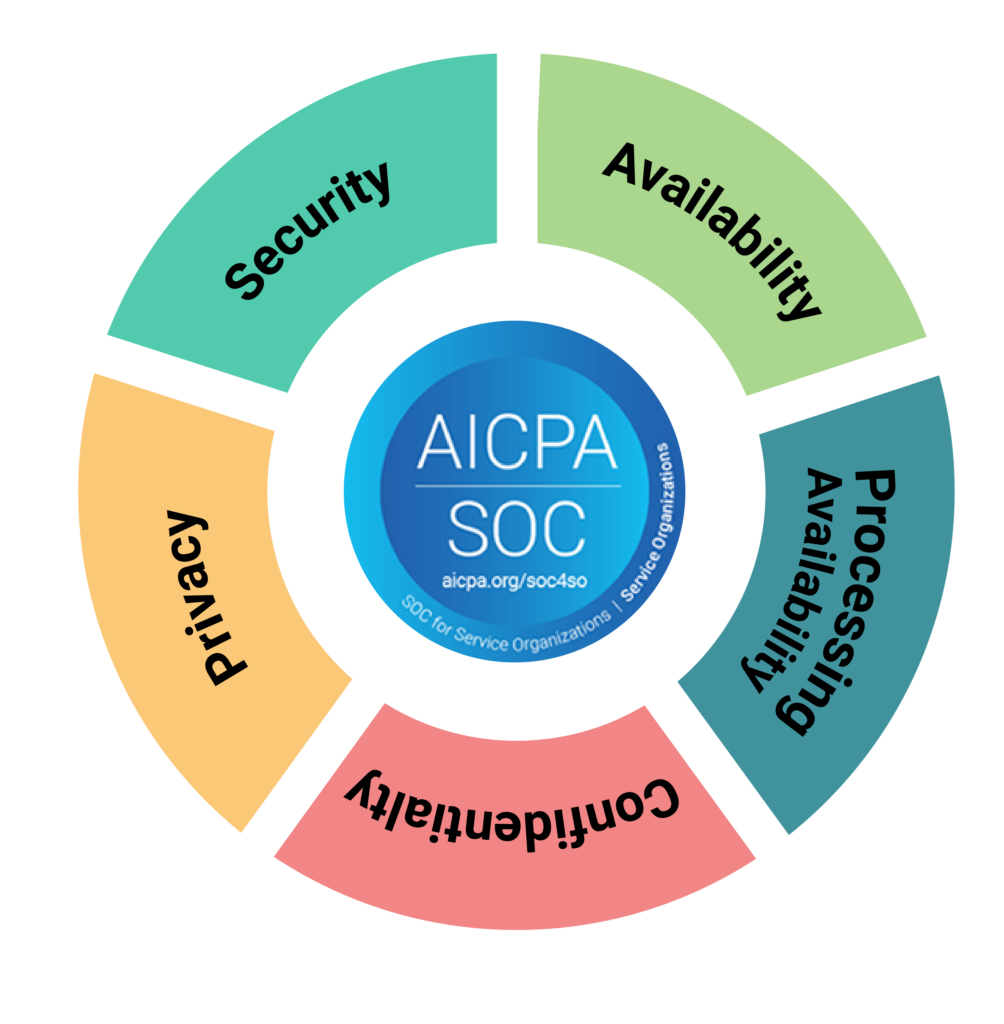
- Scoping and Trust Services Criteria selection – We help you decide which criteria (Security, Availability, Processing Integrity, Confidentiality, Privacy) are relevant to your business and customer expectations. Security is mandatory. The others depend on what you do and what your customers care about.
- Gap analysis and remediation roadmap – We assess your current controls against SOC 2 requirements, identify what is missing or insufficient, and give you a prioritised plan to get audit-ready. No generic checklists. This is tailored to your environment.
- Policies, procedures, and control documentation – SOC 2 auditors want to see documented policies, evidence of implementation, and proof that controls are operating effectively. We help you build the documentation that passes audit without creating bureaucracy for the sake of it.
- Evidence collection strategy and tooling guidance – If you are using Vanta, Drata, or another compliance platform, we help you configure it correctly and use it to automate evidence collection. If you are not using a platform, we advise on what evidence you need and how to collect it efficiently.
- Observation period management – For Type 2 audits, you need to demonstrate that your controls have been operating effectively for at least three months (typically 6-12 months). We help you manage this period, track evidence, and ensure nothing falls through the cracks.
- Audit readiness and support – We prepare you for the formal audit, brief your team on what to expect, review your evidence packs, and provide support during fieldwork. The goal is to pass on the first attempt with no surprises.
Our Process
We have guided dozens of Australian SaaS companies through SOC 2 compliance. Here is how it works.
1. Scoping and Readiness Assessment (Weeks 1-2)
We meet with your team to understand your business, technical environment, and customer requirements. We help you select the appropriate Trust Services Criteria and conduct a gap analysis against SOC 2 requirements. You leave this phase knowing exactly what needs to be done, how long it will take, and what the investment looks like.
2. Gap Remediation and Control Implementation (Weeks 3-12)
This is where the work happens. We help you close the gaps identified in the assessment: implementing missing controls, documenting policies and procedures, configuring security tooling, and building the processes required to demonstrate compliance. Depending on your starting point, this phase typically takes 2-4 months.
3. Auditor Selection and Engagement (Week 12-14)
We help you select a qualified SOC 2 auditor (a licensed CPA firm) and negotiate the scope, timeline, and fees. Choosing the right auditor matters. We have relationships with several reputable firms and can make introductions if needed.
4. Observation Period (3-12 Months)
For SOC 2 Type 2, you need to operate your controls consistently over a defined period (minimum three months, typically six). During this time, we help you collect evidence, monitor control performance, and address any issues before the auditor arrives. This is not downtime. This is when you prove your controls work.
5. Audit Fieldwork (3-5 Weeks)
The auditor conducts their examination, reviews your documentation, tests your controls, and interviews your team. We prepare you for this phase, ensure your evidence is organised and accessible, and provide support as needed. Most companies pass on the first attempt if they have prepared properly.
6. Report Issuance and Ongoing Compliance (8-10 Weeks Post-Audit)
Once fieldwork is complete, the auditor issues a draft report for your review, followed by a final SOC 2 report. You can then share this report with customers and prospects. SOC 2 is an annual process, so we also help you maintain compliance and prepare for your next audit cycle.
Who This Is For
This service is built for Australian SaaS companies, cloud service providers, and technology businesses that need SOC 2 compliance to win enterprise customers, satisfy investor requirements, or meet contractual obligations.
You are a good fit if:
- You are selling to Australian, US or international enterprise customers who require SOC 2 as part of their vendor assessment process
- You have lost deals or had procurement stall because you do not have a SOC 2 report
- Your investors, board, or key customers are asking for independent validation of your security controls
- You have purchased Vanta or Drata and need expert guidance to configure it properly, interpret requirements, and actually achieve compliance
- You want to move fast and get your first SOC 2 report within 6-12 months without hiring a full-time compliance team
- You are a growing business and need someone who understands both the technical controls and the business context
Siege Cyber is an official partner of both Vanta and Drata. If you have already invested in one of these platforms, we work within your existing tooling to provide the strategic guidance, control design, policy development, and audit readiness support that the platform alone cannot deliver. We know exactly where these platforms excel and where you still need human expertise to make the right decisions.

Why Choose Siege Cyber
20+ years of hands-on cybersecurity experience. Our Technical Director, Peter Stewart, has spent over two decades working in information security, from network engineering to SOC 2 audit preparation. We understand security at a technical level and can translate that into the compliance language auditors expect.
Official Vanta and Drata partner. We are one of a small number of Australian consultancies officially recognised by the two leading compliance automation platforms. If you are using either tool, we know how to use it effectively and where you still need expert input to achieve compliance.
We understand the Australian context. SOC 2 originated in the United States, but Australian companies face unique considerations around the Privacy Act 1988, APRA CPS 234, and cross-border data requirements. We help you align SOC 2 with the broader regulatory obligations that apply to Australian businesses.
No box-ticking, no compliance theatre. We care about real security outcomes, not just passing audit. The controls we help you implement will satisfy auditors, but they will also genuinely improve how you manage risk and protect customer data. That is the whole point.
We have been through this process dozens of times. We know what auditors look for, which controls matter most, and where companies typically get stuck. You get the benefit of our experience without having to learn the hard way.
Frequently Asked Questions
Should we pursue SOC 2 Type 1 or Type 2?
Type 1 is a point-in-time assessment that shows your controls were designed properly and in place on a specific date. Type 2 demonstrates that your controls operated effectively over a period of time (typically 6-12 months). Almost all enterprise customers expect Type 2 because it provides much stronger assurance. We generally recommend going straight to Type 2 unless you need something quickly for a specific deal.
How long does it take to get SOC 2 compliant?
For most Australian SaaS companies, the full process from kickoff to receiving your SOC 2 Type 2 report takes between 8 and 15 months. This includes 3-4 months of preparation, 6-12 months of observation, and 2-3 months for audit and report issuance. Type 1 can be faster (3-6 months) because there is no observation period. Your timeline depends on the maturity of your existing controls and how quickly you can implement changes.
Do we need to include all five Trust Services Criteria?
No. Security is mandatory. The other four (Availability, Processing Integrity, Confidentiality, Privacy) are optional and depend on your business and what your customers expect. Most SaaS companies include Security and Availability as a minimum. If you handle sensitive data or have specific customer requirements, you may also include Confidentiality or Privacy. We help you decide based on your actual needs, not a one-size-fits-all approach.
What happens if we fail the audit?
If the auditor identifies control deficiencies during fieldwork, they will document them in the final report as exceptions. Minor exceptions do not necessarily mean failure, but they do weaken the report and may concern customers. Significant deficiencies may require remediation and additional testing before the auditor can issue the report. We prepare you thoroughly to minimise the risk of exceptions, and most of our clients receive clean reports on the first attempt.
Can we get SOC 2 compliant without Vanta or Drata?
Yes. Platforms like Vanta and Drata make evidence collection and monitoring much easier, but they are not required. You can achieve SOC 2 compliance manually by documenting controls, collecting evidence, and managing the process yourself. That said, most companies find the investment in a compliance platform worthwhile because it saves significant time and reduces the risk of missing evidence during audit.
How much does a SOC 2 audit cost?
Auditor fees typically range from $15,000 to $50,000+ depending on the scope, number of Trust Services Criteria, complexity of your environment, and the auditor you choose. This does not include the cost of compliance platforms, consulting support, or internal effort. We help you understand the full investment during the scoping phase and can introduce you to auditors with transparent pricing.
Do we need SOC 2 if we already have ISO 27001?
SOC 2 and ISO 27001 serve different markets. ISO 27001 is recognised globally and often required by European and Australian enterprises. SOC 2 is the standard for US enterprise customers. If you are selling into both markets, you may need both certifications. The good news is that much of the work overlaps, and we can help you align the two frameworks to avoid duplication.
Ready to Get SOC 2 Compliant?
SOC 2 compliance opens the door to enterprise deals, shortens procurement cycles, and gives your customers confidence that their data is secure. The sooner you start, the sooner you can stop losing opportunities because you do not have the report your prospects expect.
Book a free 30-minute consultation with our team. We will assess your current state, explain what is involved, and give you a clear roadmap to compliance with no obligation. You will leave the call knowing exactly what needs to happen and whether Siege Cyber is the right partner to get you there.
