What Is the SOCI Act? Guide for Australian Businesses
The Security of Critical Infrastructure Act 2018, commonly called the SOCI Act, is Australian federal legislation that sets out the legal obligations for organisations that own, operate, or hold direct interests in critical infrastructure assets. If your organisation operates in one of the eleven sectors covered by the Act, you are likely a responsible entity with real compliance obligations. Understanding what the SOCI Act requires, who it applies to, and what happens if you do not meet your obligations is essential for any business that may fall within its scope.
The Act has been significantly expanded since it commenced in 2018. What originally covered electricity, gas, water, and ports now spans 22 asset classes across 11 sectors of the economy. That expansion means many organisations that did not think the SOCI Act applied to them are now covered, including technology companies, SaaS providers, data centres, and businesses in sectors like financial services, healthcare, and logistics.

Who Does the SOCI Act Apply To?
The question of who the SOCI Act applies to depends on two things: whether your organisation operates in a covered sector, and whether you meet the definition of a responsible entity or direct interest holder for a critical infrastructure asset.
The eleven sectors covered by the Act are:
-
Communications
-
Data storage and processing
-
Defence industry
-
Higher education and research
-
Energy (electricity, gas, liquid fuels)
-
Financial services and markets
-
Food and grocery
-
Healthcare and medical
-
Space technology
-
Transport (aviation, maritime, road, rail)
-
Water and sewerage
A responsible entity is an organisation that owns or operates a critical infrastructure asset. A direct interest holder is an entity that holds a legal or equitable interest of 10% or more in a critical infrastructure asset, or that has a position that gives it the ability to influence or control that asset. Both types of entities carry compliance obligations under the Act.
It is worth noting that not all 22 asset classes trigger every obligation. Some obligations, particularly the Critical Infrastructure Risk Management Programme (CIRMP) requirement, apply only to specific asset classes. If you are uncertain whether your organisation is covered, the Cyber and Infrastructure Security Centre (CISC) publishes a compliance table on their website that maps obligations to asset classes.
The CIRMP: What It Is and Why It Matters
The Critical Infrastructure Risk Management Programme is the centrepiece of SOCI Act compliance for responsible entities. Under Part 2A of the SOCI Act, responsible entities for specified critical infrastructure assets must have a written CIRMP in place, comply with it, and have it signed off by their board.
The CIRMP must address four key hazard vectors:
-
Cyber and information security – risks to digital systems, computers, datasets, and networks that underpin critical infrastructure
-
Personnel security – insider threats and risks posed by workers with access to critical assets
-
Supply chain security – vulnerabilities introduced through third-party vendors, suppliers, and service providers
-
Physical security – risks from unauthorised access, sabotage, natural disasters, and physical breaches
The cyber security hazard vector is the largest and most technically complex of the four. It requires your CIRMP to be underpinned by a recognised security framework, such as ISO 27001, the NIST Cybersecurity Framework, or the ASD Essential Eight. This is where most organisations run into difficulty, because building a defensible cyber programme that meets CIRMP requirements and stands up to scrutiny is not a documentation exercise. It requires real implementation of controls, active risk management, and evidence that your programme is working.
The CIRMP must be reviewed annually, reported on to your board, and updated as your environment and risk profile change. That ongoing commitment is what distinguishes SOCI Act compliance from a one-time certification exercise.
If you are not sure whether your organisation needs a CIRMP, or which framework your cyber security obligations should be built on, a brief consultation is a good starting point. Siege Cyber provides free initial conversations to help organisations work out exactly where they stand under the SOCI Act and what their obligations look like in practice. Get in touch at [email protected].
Mandatory Cyber Incident Reporting
One of the most immediate and time-sensitive obligations under the SOCI Act is mandatory cyber incident reporting. Responsible entities must report cyber security incidents to the Australian Cyber Security Centre (ACSC) within strict timeframes.
For critical cyber security incidents, defined as those having a significant impact on the availability of your asset, you must notify the ACSC within 12 hours of becoming aware of the incident. For other cyber security incidents that have had, are having, or are likely to have a relevant impact on your asset, the reporting window is 72 hours.
These timeframes are not aspirational targets. Failing to meet them is a breach of the Act and may attract penalties. That means you need incident detection and response capabilities in place before an incident occurs, not after. An incident response plan that sits in a folder and has never been tested will not help you meet a 12-hour reporting deadline under real-world pressure.
What Happens If You Do Not Comply?
The SOCI Act includes real penalty provisions for organisations that fail to meet their obligations. For corporations, financial penalties range from $82,500 to $412,500 depending on the nature of the breach. Beyond financial penalties, the regulator can issue enforceable undertakings, seek injunctions, and exercise monitoring and inspection powers.
SOCI Act compliance audit obligations are also real. The Cyber and Infrastructure Security Centre has authority to assess an entity’s compliance, including requesting information about your CIRMP and how it is being implemented. A SOCI Act compliance audit that finds your CIRMP is incomplete, not genuinely implemented, or that your board cannot demonstrate oversight of cyber risk is a serious outcome.
The regulator has signalled that it expects meaningful compliance, not paperwork compliance. As the Act matures and enforcement activity increases, the distinction between organisations that have genuinely implemented their CIRMP and those that have produced a document without embedding it into operations will become more visible.
The Sectors Most Likely to Encounter SOCI Act Obligations
Two sectors worth calling out specifically are data storage and processing, and financial services.
Data storage and processing is an asset class that catches many technology companies and SaaS providers off guard. If your organisation stores or processes data that supports the operation of critical infrastructure, or if you operate data centre infrastructure, you may fall within this class even if you do not think of yourself as critical infrastructure. This has been a consistent source of surprise for technology businesses that have only recently been notified by the Department of Home Affairs that the Act applies to them.
Financial services and markets is another sector where obligations have expanded, including the addition of critical payment systems following recent rule amendments. If you operate payment infrastructure, financial market systems, or manage assets in the financial sector, the CIRMP obligations and incident reporting requirements apply to you.
How Siege Cyber Helps with SOCI Act Compliance
Siege Cyber focuses specifically on the cyber security and information security hazard vector of your CIRMP. That is where our expertise sits, and it is the vector that requires the most technical depth to implement properly.
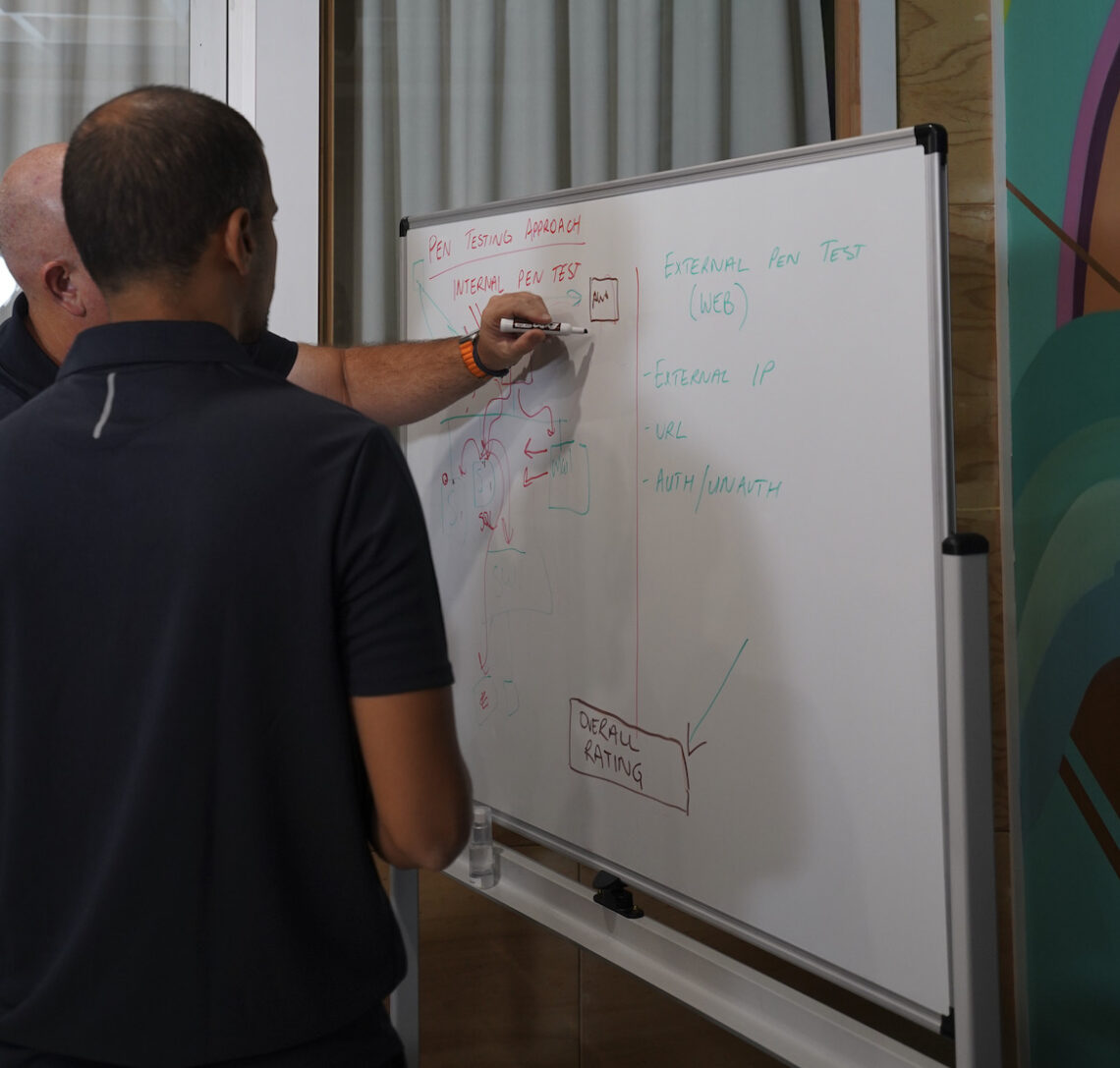
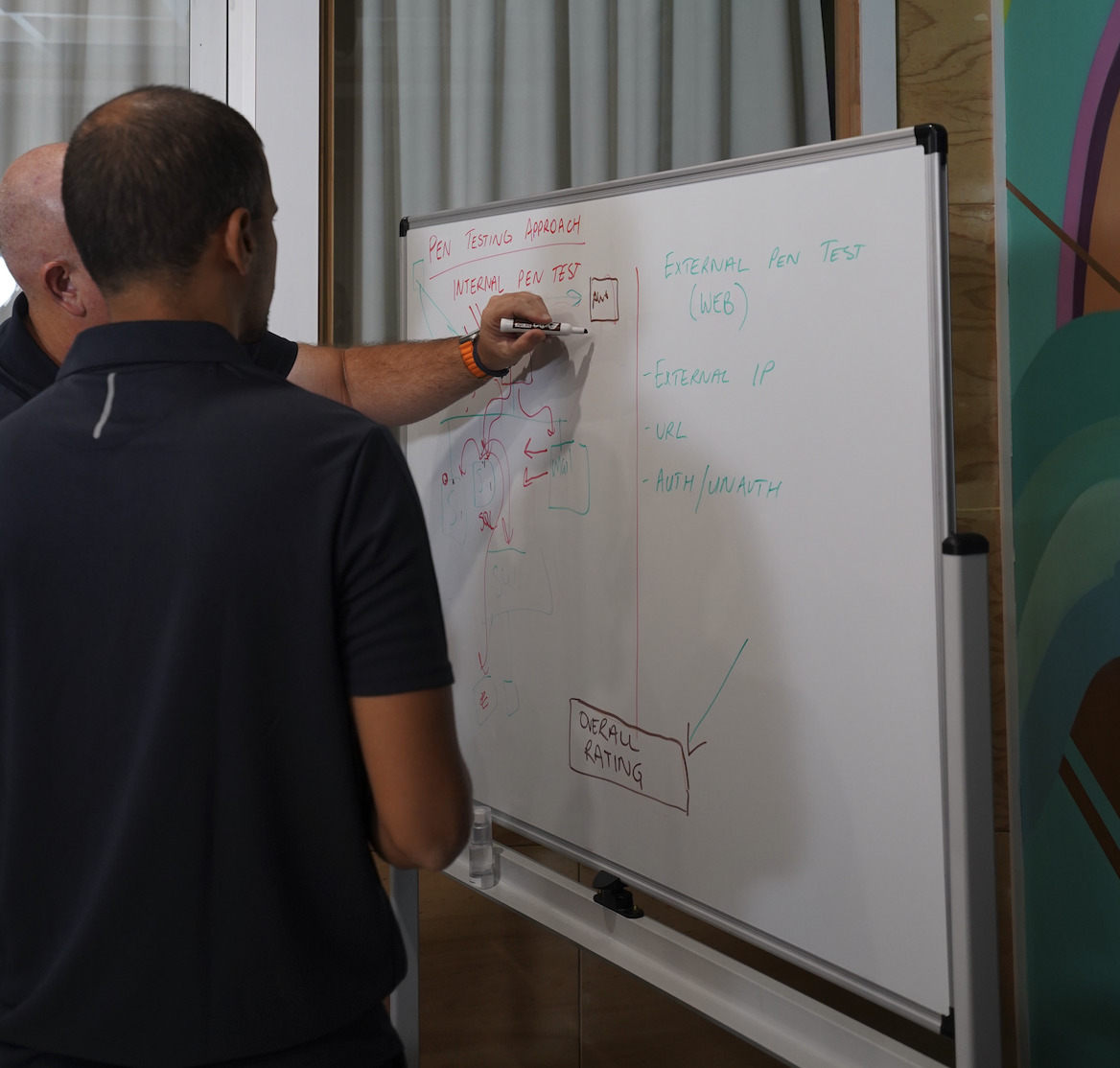
We help organisations work through the full cyber pillar of their CIRMP, from the initial gap analysis to control implementation, penetration testing and validation, incident response planning built to meet the 12-hour and 72-hour reporting obligations, and the quarterly cyber risk reporting your board is required to review. We are transparent about what falls within our scope and what requires a specialist in physical security, personnel vetting, or operational technology.
We work well with technology companies, SaaS providers, and data storage operators, mid-sized businesses in regulated sectors, and boards that have received a notification from the Department of Home Affairs and need a clear, practical response. You do not need to have everything sorted before you reach out. Most of our clients come to us at the start of the process, when they are still working out what the SOCI Act actually requires of them.
Visit siegecyber.com.au to see how we support Australian critical infrastructure operators, or get in touch directly at [email protected]. The first conversation is free, and there is no commitment required.