
SOC 2 for Australian SaaS Companies: Why Your Customers Are Asking for It
If you run a SaaS business in Australia and you are selling into enterprise accounts or US-based customers, there is a good chance someone has already asked you for your SOC 2 report. SOC 2 compliance in Australia is no longer a niche requirement reserved for large tech companies – it has become a standard part of the procurement process, and the requests are only getting more frequent.
So what is it, why do your customers want it, and what does it actually take to get there?
What SOC 2 Is (and What It Is Not)
SOC 2 stands for System and Organisation Controls 2. It is a framework developed by the American Institute of Certified Public Accountants (AICPA) that sets out how service providers should manage and protect customer data.
Unlike ISO 27001, which is a certifiable standard with an international presence, SOC 2 is an attestation. That means an independent auditor examines your controls and issues a report confirming whether your systems and processes meet the relevant criteria. There is no badge or certificate per se – you get a report, and you share it with customers or prospects under a non-disclosure agreement.
There are two types of SOC 2 reports:
-
Type I – A point-in-time assessment. It confirms that your controls are designed appropriately as at a specific date.
-
Type II – Covers a period of time (typically six to twelve months) and tests whether those controls actually operated effectively throughout that period. This is the one most enterprise customers want.
Why Australian SaaS Companies Are Being Asked for It
The short answer is that enterprise procurement teams have become more security-conscious, and SOC 2 has become their preferred shortcut for evaluating vendor risk.
Rather than asking you to fill out a 200-question security questionnaire from scratch, a prospective customer can request your SOC 2 report and get a standardised, auditor-verified view of your security posture. It saves them time and gives them more confidence than a self-assessment ever could.
Australian SaaS companies selling into the US market have been dealing with these requests for a few years now. But the pattern has spread. Large Australian enterprises, government-adjacent bodies, and businesses operating under frameworks like APRA CPS 234 are increasingly using SOC 2 reports as part of their vendor due diligence – even when the vendor is local.
If you are in the business of handling customer data (and most SaaS companies are), a prospect’s security team will eventually ask the question.
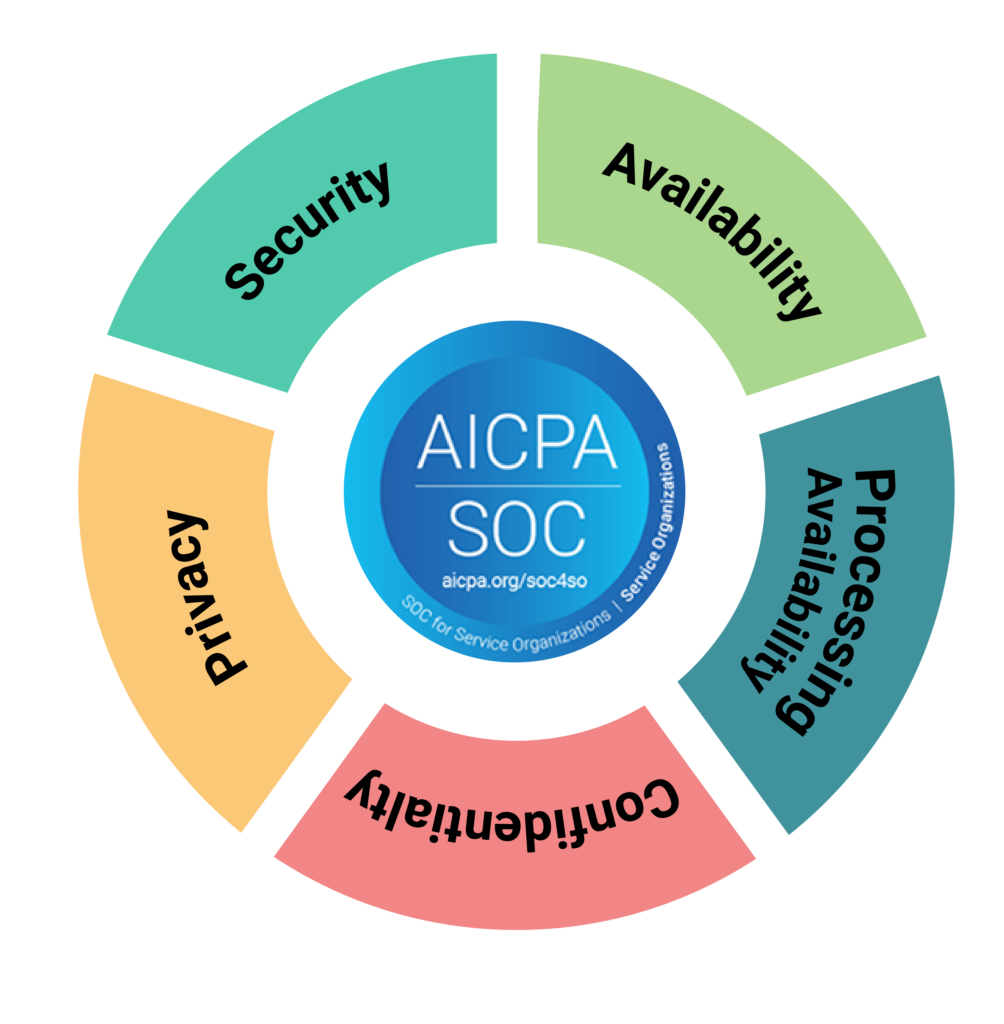
The Five Trust Service Criteria
SOC 2 assessments are built around what the AICPA calls the Trust Service Criteria. Security (also called the Common Criteria) is mandatory. The others are optional and can be included based on what is relevant to your business:
-
Security – Protection of systems and data against unauthorised access
-
Availability – Systems are available for operation as agreed
-
Processing Integrity – System processing is complete, valid, and accurate
-
Confidentiality – Information designated as confidential is protected appropriately
-
Privacy – Personal information is handled in line with the organisation’s commitments
Most SaaS companies start with Security only. If you have contractual uptime commitments or handle sensitive personal data, you might add Availability or Privacy. This is something worth discussing with your auditor or advisory partner before you decide on scope.
Not sure whether SOC 2 or ISO 27001 is the right fit for your business? They serve different purposes and different audiences, and choosing the wrong one can cost you time and money. Siege Cyber can help you work through the decision as part of a scoping consultation. View our SOC 2 services or explore our compliance pricing.
What the SOC 2 Readiness Process Actually Looks Like
Most organisations are not ready for a SOC 2 audit the moment they decide they want one. That is normal. The readiness phase is where most of the real work happens.
Readiness typically involves:
-
Scoping the assessment – deciding which Trust Service Criteria apply and which systems are in scope
-
Gap analysis – identifying where your current controls fall short of what the criteria require
-
Remediation – building or updating policies, controls, and procedures to close the gaps
-
Evidence collection – gathering documentation that demonstrates your controls are operating
-
Audit – engaging an accredited CPA firm to conduct the formal assessment and issue the report
The timeline varies depending on your starting point, but most organisations take three to six months to get from gap analysis to a completed Type II report.
One thing worth knowing: compliance automation platforms like Vanta and Drata have made this process significantly more manageable. They connect to your existing tech stack, pull evidence automatically, and track your progress against the SOC 2 criteria in real time. Siege Cyber is an official partner of both platforms, which means we can help you get the most out of whichever one you choose.
The platforms handle a lot. But they do not replace the human expertise needed to interpret the criteria, make decisions about scope, write policies that hold up under audit, or prepare your team for auditor interviews. That is where we come in.
Common Mistakes Australian SaaS Companies Make
The most common mistake is underestimating the evidence burden. Controls need to be documented and demonstrably in operation throughout the audit period. Saying “we do that” is not enough – the auditor needs to see it.
The second most common mistake is scoping too broadly on the first pass. Including every system and sub-processor in scope makes the process longer, more expensive, and harder to manage. Start focused, get your Type II report, and expand scope in future cycles if needed.
The third is confusing readiness with compliance. Being told by a platform that you are “90% ready” is not the same as being audit-ready. An experienced adviser will tell you which gaps actually matter and which ones can be addressed after the report is issued.

SOC 2 and Australian Privacy Obligations
If you handle personal information, your SOC 2 Privacy criterion overlaps directly with your obligations under the Privacy Act 1988. Australia’s Privacy Act has recently undergone significant reform proposals, with the government pushing for stronger data security requirements and broader individual rights. Pursuing SOC 2 compliance can strengthen your position under both frameworks – particularly if your Privacy criterion covers how personal data is collected, stored, and deleted.
It is also worth noting that if you are a SaaS vendor selling into financial services customers, those customers may be subject to APRA CPS 234, which requires regulated entities to manage third-party security risk. A SOC 2 Type II report is one of the cleaner ways to satisfy that requirement on their behalf.
If your customers are asking for SOC 2 and you are not sure where to start, talk to Siege Cyber. We work with Australian SaaS companies through every stage of the process – from scoping and gap analysis through to audit preparation and ongoing compliance. Visit siegecyber.com.au/services/soc2 to learn more, view our pricing, or reach out to us at [email protected].