
SOC 2 Audit Process: A Practical Walkthrough
If you’re weighing up whether SOC 2 is worth it for your business, it can feel hard to get your head around. The SOC 2 audit process is structured and predictable if you know what’s coming and how to prepare.
This walkthrough will take you behind the scenes so you can see what auditors do, what they expect from you and how to get through the process without burning your team out.

what SOC 2 covers
SOC 2 is a widely recognised framework used by service providers to prove they manage customer data securely and reliably. It is built around the Trust Services Criteria: security, availability, processing integrity, confidentiality and privacy.
While it was originally developed in the US, SOC 2 has become the de facto standard many overseas customers expect. For Australian SaaS and technology businesses, it complements existing obligations under the Privacy Act 1988, APRA CPS 234 and the ASD Essential Eight.
There are two main report types you will hear about:
-
Type I looks at the design of your controls at a point in time.
-
Type II looks at how well those controls operated over a period, usually 3 to 12 months.
The audit steps are similar, but a Type II goes deeper into evidence and consistency over time.
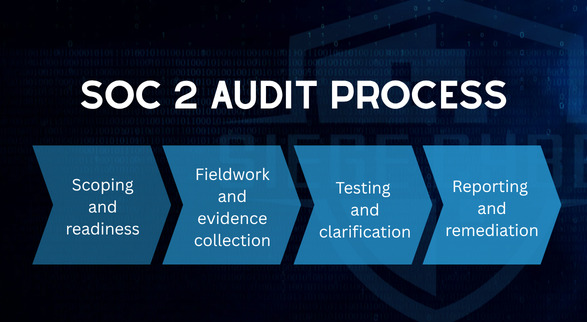
The SOC 2 audit process at a glance
Most SOC 2 audits follow the same broad stages:
-
Scoping and readiness.
-
Fieldwork and evidence collection.
-
Testing and clarification.
-
Reporting and remediation.
Different audit firms might use slightly different language, but the flow is much the same. Understanding each stage makes the whole SOC 2 compliance audit feel far less mysterious.
Step 1: Scoping and readiness
Before anyone reviews a single control, you need to agree on what is in scope.
Typical scoping questions include:
-
Which systems and services are included?
-
Which Trust Services Criteria apply to your business?
-
Which locations, cloud environments and third parties are covered?
This is where a lot of pain can be avoided. Poor scoping either blows out effort and cost, or leaves out systems that customers care about.
Most mature organisations also run a readiness assessment before the formal SOC 2 audit begins. That might include:
-
Reviewing current policies, procedures and technical controls.
-
Mapping what you already do against SOC 2 requirements.
-
Identifying gaps and creating a remediation plan.
-
Allocating an owner for each control.
If you are using Vanta or Drata, this is where the platforms can help you automate evidence collection and keep track of control status. The missing piece is interpretation and judgement. Siege Cyber works with both platforms as an official partner, and we focus on tuning the control set so it matches how your business actually operates, rather than blindly accepting every default control as-is.
If you are not sure whether you are audit ready, a structured SOC 2 gap analysis is often the best first step. Siege Cyber offers this as a standalone engagement so you can understand your starting point before committing to audit costs.
Step 2: Fieldwork and evidence collection
Once scope is agreed and your audit period is set (for Type II), the auditor begins fieldwork. This is where they test whether you do what you say you do.
Expect a combination of:
-
Document reviews: policies, procedures, risk registers, incident response plans, change management records and training logs.
-
Technical evidence: screenshots, configurations from systems like AWS, Azure, GCP, identity providers, logging platforms and security tools.
-
Samples: for a control that should happen regularly (for example, user access reviews every quarter), the auditor will pick samples from the audit period and ask you to prove they occurred.
For many companies, this is the most time consuming part of the soc 2 audit process. The better your internal documentation and evidence workflows, the less scramble there is.
This is also where compliance automation tools can materially reduce effort by pulling logs and screenshots on a schedule. Siege Cyber helps clients configure Vanta and Drata so the right evidence is collected with minimal manual chasing, while still aligning that evidence with SOC 2 expectations rather than just ticking software boxes.
Step 3: Interviews, walkthroughs and testing
Fieldwork is not just email requests for screenshots. Auditors will also want to speak to key people and see how controls work in practice.
Common examples include:
-
Walking through how you onboard and offboard staff, including access provisioning and revocation.
-
Demonstrating how you handle security incidents, from detection through to notification and lessons learned.
-
Showing how changes to production systems are requested, approved, tested and deployed.
-
Explaining how you manage third-party risk and vendor security reviews.
These sessions give the auditor context and help them assess whether the control environment is real or just nice words in a policy.
Your job is to be clear, honest and consistent. If there are known weaknesses, it is far better to explain how you are addressing them than to pretend they do not exist.
If you do not already have a structured security programme in place, this is often where gaps show. Many Australian businesses lean on ISO 27001-style governance, ASD Essential Eight uplift work or similar frameworks to provide the underlying discipline that supports SOC 2.
Step 4: Findings, exceptions and the SOC 2 report
After testing is complete, the auditor pulls everything together in the SOC 2 report.
The report typically includes:
-
A description of your system and the scope of the engagement.
-
The auditor’s opinion on whether your controls were suitably designed (and, for Type II, operated effectively over the review period).
-
Any exceptions, deviations or notable weaknesses found during testing.
-
Management’s response to those issues.
Not every exception is the end of the world. A single missed quarterly access review, for example, can often be explained and put in context. Patterns of poor practice are more serious and can affect how customers interpret your report.
The most valuable outcome, apart from the report itself, is often the list of improvement actions. Treat the SOC 2 audit as a chance to strengthen your security practice, not just as a pass/fail badge for sales.
If you want support interpreting findings or prioritising remediation, this is an area where an external cybersecurity partner adds real value.

How long does a SOC 2 compliance audit take?
The total timeline depends on your audit period, your readiness and how quickly you can supply evidence.
Broadly:
-
Readiness and remediation can take anywhere from 2 to 6 months, depending on maturity.
-
A Type I audit is usually completed over several weeks once you are ready.
-
A Type II audit requires an operating period (for example, 6 or 12 months), plus a similar fieldwork and reporting phase.
A common pattern for growing SaaS companies is to do a Type I once controls are in place, then follow with a Type II once those controls have been running consistently.
If you want a sense of effort and cost before you commit, Siege Cyber publishes transparent compliance pricing so you can budget without guesswork.
Where Siege Cyber fits into your SOC 2 journey
You do not have to choose between doing everything yourself or outsourcing the entire process to an auditor.
Siege Cyber supports Australian businesses throughout the SOC 2 audit process by:
-
Running readiness and gap assessments so you know exactly what needs to change.
-
Helping you design and implement practical controls that align with SOC 2, ISO 27001 and the ASD Essential Eight.
-
Working with your chosen auditor to clarify evidence requests and keep the process moving.
-
Tuning and operating platforms like Vanta and Drata so the automation works with your environment, not against it.
Midway through your SOC 2 journey and feeling unsure if you are on track? A short advisory engagement or independent review can save you months of back and forth later.
For an overview of how Siege Cyber can help with SOC 2 readiness and audit preparation, visit our website.

Ready to make your SOC 2 audit boring (in a good way)?
A SOC 2 compliance audit does not have to take over your year. With a clear scope, sensible controls and the right support, it becomes another piece of your broader security story, alongside your privacy obligations, APRA or ASIC expectations and Essential Eight uplift work.
If you would like help getting ready for SOC 2, reviewing your current control set or using Vanta or Drata effectively, reach out at siegecyber.com.au or email [email protected] to book a short discussion. You will walk away with a realistic view of effort, cost and the next steps that make sense for your organisation.