
Network Penetration Testing Services in Australia
If your organisation relies on a corporate network, you are already a target. Network penetration testing services give you a safe way to see how an attacker could break in, before someone actually does. Done properly, penetration testing for Australian businesses also supports obligations under the Privacy Act, the Notifiable Data Breaches scheme, APRA CPS 234 and the ASD Essential Eight.
In 2024, the Office of the Australian Information Commissioner reported 1,113 notifiable data breaches in Australia, a 25% increase on the previous year. A large share of these incidents start with basic network weaknesses that could have been found and fixed with structured testing.

What network penetration testing services actually do
At a simple level, network penetration testing is a controlled security attack on your environment, carried out by qualified ethical hackers under a contract and a clear scope. The goal is to show how far someone could get through your firewalls, VPNs, wireless networks and internal systems and what that would mean for your data and operations.
For Australian businesses, this is a security essential, not a discretionary exercise. APRA CPS 234 expects regulated entities to systematically test the effectiveness of their information security controls, including independent specialist testing. The ASD Essential Eight also assumes that you are validating whether your controls are actually working, not just written down in a policy.
If you want more depth on how penetration testing fits within your broader security posture, Siege Cyber’s main penetration testing services page is a good next read.
Types of network penetration testing for Australian businesses
Most penetration testing services in Australia will offer several flavours of network testing. At Siege Cyber, we commonly deliver:
-
External network penetration testing (testing your internet-facing systems such as firewalls, VPN gateways, remote access portals and exposed services).
-
Internal network penetration testing (assessing what an attacker or malicious insider could do once on the internal network, including lateral movement and privilege escalation).
-
Wireless penetration testing (reviewing guest and corporate Wi‑Fi, encryption, authentication and common configuration weaknesses).
-
Cloud and hybrid network testing (Azure, AWS and other cloud platforms, as well as the links between your on-premises environment and cloud services).
Many organisations now have a mix of office networks, remote users and cloud platforms, so a modern engagement typically blends several of these, rather than treating each in isolation.
What is included in a professional network penetration test
Not all penetration testing services in Australia are equal. If you are buying purely on price, you may only get an automated scan and a generic report. A thorough engagement should include:
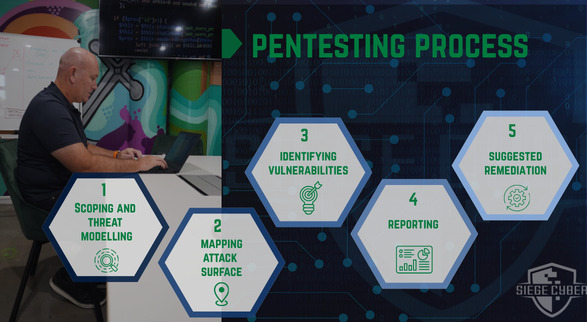
1. Scoping and threat modelling
A proper test starts with a conversation, not a scan. The tester should work with you to understand:
-
Business context and critical assets (for example, patient records, payment systems, IP, OT networks).
-
Regulatory drivers such as Privacy Act, CPS 234, PCI DSS or sector-specific guidance.
-
Your current control environment, including firewalls, network segmentation, VPN, MFA and monitoring.
This “threat modelling” step shapes a test that reflects how real attackers are likely to target your organisation, rather than a tick-box exercise.
2. Reconnaissance and mapping your attack surface
The team will then identify what is exposed. This usually covers:
-
External asset discovery (domains, IP ranges, cloud services and third-party endpoints).
-
Internal network discovery (subnets, key servers, directory services and trust relationships).
For many clients, this step alone is eye-opening, as it often uncovers forgotten systems, legacy VPN endpoints or test environments that were never properly locked down.
3. Vulnerability identification and exploitation
Automated vulnerability scanners are useful, but they are only the starting point. A quality penetration testing service will:
-
Run targeted scans to identify missing patches, weak services and misconfigurations.
-
Manually validate and exploit key issues to understand real-world impact, not just theoretical risk.
-
Chain multiple smaller weaknesses together to see how far an attacker could go (for example, from an exposed service to domain admin to sensitive data).
This manual exploitation and chaining is what separates genuine penetration testing from a simple vulnerability assessment.
4. Mapping against Essential Eight and compliance obligations
For Australian businesses, it is useful to see findings translated into the language of local frameworks. A good report will link technical issues back to:
-
ASD Essential Eight maturity levels, so you can see whether weaknesses are blocking you from reaching Level 1, 2 or 3 for specific controls.
-
APRA CPS 234 expectations for testing and assurance of information security controls, if you are regulated.
-
Privacy Act and Notifiable Data Breaches obligations, highlighting any clear pathways to unauthorised access to personal information.
This helps you explain the findings to your board or regulator in terms they already recognise.
5. Clear, prioritised reporting and remediation guidance
At the end of the engagement, you should receive:
-
An executive summary in plain language, describing how you could be compromised and what that would mean.
-
A detailed technical section with each finding, evidence, likelihood and impact.
-
Practical remediation advice that your IT team or MSP can act on, including configuration changes, patching requirements and design improvements.
This is where Siege Cyber spends a lot of time. The value is not just in finding issues, but in helping you fix them quickly and efficiently.
If you are not sure whether you need full penetration testing yet, a shorter security gap analysis or Essential Eight assessment can be a sensible way to get a baseline on your current posture. Siege Cyber offers these as standalone services for organisations that want a clear roadmap before committing to a broader testing programme.
How often should Australian businesses run penetration testing?
There is no single answer, but there are some clear patterns.
APRA CPS 234 expects APRA-regulated entities to have systematic testing, including independent specialist testing, at least annually or when there is material change to information assets or the business environment. For many non-regulated organisations, annual network penetration testing is a sensible baseline, with additional testing after major changes such as:
-
New cloud platforms or major migrations.
-
Mergers and acquisitions or integration of new networks.
-
Introduction of internet-facing services like new customer portals or remote access solutions.
If you are working towards ISO 27001 or SOC 2, regular penetration testing also feeds into your ongoing risk assessment and control validation, and provides evidence to auditors that you are not relying solely on paper-based controls.
How Siege Cyber approaches penetration testing services in Australia
Siege Cyber is a Brisbane-based cyber security firm that specialises in penetration testing for Australian businesses of all sizes, from fast-growing startups through to regulated financial and health organisations. Our team combines hands-on testing experience with strong knowledge of compliance frameworks such as ISO 27001, SOC 2 and the ASD Essential Eight.
A few things that set our network penetration testing services apart:
-
We scope tests around your real risks, not just the number of IP addresses.
-
We focus on manual testing and exploitation by experienced consultants, not just running tools.
-
We write reports in plain English, with clear recommendations and prioritisation so you know what to fix first.
For clients using compliance automation platforms like Vanta or Drata, we also act as the human partner that turns automated findings into an actionable security improvement plan. These platforms are excellent at tracking policies and control evidence, but they do not replace independent penetration testing to validate that your network is actually secure in practice.
You can see a high-level overview of Siege Cyber’s penetration testing offerings and typical engagement models on our penetration testing services page.
What does network penetration testing cost?
Penetration testing services in Australia vary in price based on scope, complexity and regulatory requirements. A small external network test will be at the lower end, while a large internal, cloud and wireless engagement for an APRA-regulated entity will naturally require more effort.
To keep things transparent, Siege Cyber publishes guideline pricing bands for common penetration testing packages on our website, so you can quickly see what ballpark you are in before you speak to us. You can review those options here: siegecyber.com.au/#pentest-pricing.
If you need something more tailored, such as ongoing quarterly testing or combined network, application and API testing, we regularly build custom packages for clients and can walk you through the options in a short call.
Why network penetration testing matters now
The steady rise in reported data breaches in Australia shows that attackers are still finding and exploiting basic weaknesses. In 2024 alone, 1,113 data breach notifications were made to the OAIC, the highest yearly total since mandatory reporting began. Many of those incidents involved malicious or criminal attacks rather than accidental disclosure, which highlights the need for proactive testing rather than reactive clean-up.
Network penetration testing services help you:
-
Find and close high-risk holes before someone else does.
-
Demonstrate to regulators, customers and auditors that you are taking reasonable steps to protect information.
-
Prioritise your security budget on the fixes that actually reduce risk, instead of buying more tools that may not address the root causes.
For many Australian organisations, a structured penetration test has been the moment that turned cyber security from an abstract concern into a clear, actionable plan.

Ready to talk about penetration testing?
If you are responsible for security, IT or risk in your organisation and you are unsure how exposed your network really is, a network penetration test is one of the most direct ways to get clarity. Siege Cyber’s consultants are happy to walk you through what an engagement would look like for your environment, with no obligation.
Visit siegecyber.com.au, review our penetration testing services and indicative pentest pricing, then get in touch via the contact form or email [email protected] to book a short, practical discussion about your options.