ISO 27001 vs Essential Eight: Which Framework Is Right for Your Australian Business?
If you are weighing up ISO 27001 vs Essential Eight for your Australian business, you are not alone. Many boards and executives are being pushed to do something about cyber risk, but it is not always clear which framework actually fits their size, sector and budget.
This post will walk through what each framework does, how they differ and how to decide which one (or combination) makes sense for you in Australia.
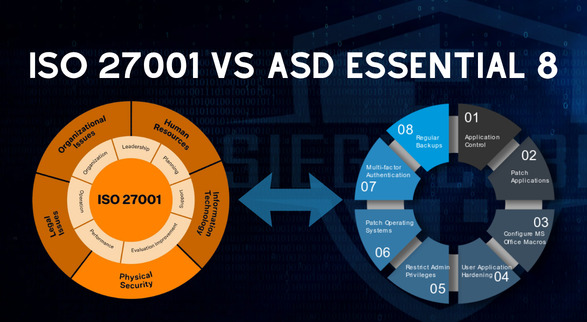
Quick overview: ISO 27001 and Essential Eight in Australia
ISO 27001 is an international standard for building and running an Information Security Management System (ISMS). It is risk based, broad in scope, and designed so you can be independently certified by an accredited auditor.
Essential Eight is an Australian Signals Directorate (ASD) set of eight technical mitigation strategies, with a maturity model that outlines how well you have implemented them. It comes from the Australian Cyber Security Centre (ACSC) and is positioned as a practical baseline for lifting cyber resilience across government and private sector.
In short, ISO 27001 is a management system across your whole organisation; Essential Eight is a focused set of technical controls, mainly on your Microsoft‑centric infrastructure and endpoints.
ISO 27001 vs Essential Eight: key differences
Scope and depth
- ISO 27001
-
-
Covers governance, risk management, roles and responsibilities, policies, supplier risk, incident management, awareness training, and a broad Annex A control set.
-
Applies to any type of organisation and you choose the scope (eg. whole business or particular services).
-
-
Essential Eight
-
Focuses on eight technical areas such as application control, patching, macro security, restricting admin privileges, and daily backups.
-
Originally aimed at government systems, but now strongly recommended by ACSC for all Australian organisations as a baseline.
-
If you need a structured, auditable system that touches every part of the business, ISO 27001 does that. If you want to lift your technical defences quickly in a measurable way, Essential Eight is designed for that.
Certification and expectations
-
ISO 27001 allows you to obtain formal certification from a JAS‑ANZ accredited certification body, which can be a tender or contractual requirement in its own right.
-
Essential Eight is used as a maturity model (Levels 0 to 3) and is mandatory at certain levels for many Australian Government systems; in the private sector it is often used as an expected baseline or audit yardstick.
For APRA‑regulated entities working to CPS 234, ISO 27001 can help demonstrate a structured approach to information security, while Essential Eight helps show that key technical controls are implemented and monitored.
Effort, cost and time
ISO 27001 generally requires more upfront effort: defining scope, conducting risk assessments, creating and maintaining policies and procedures, evidence of monitoring, and internal audits. It is not a quick project, especially if you are starting from a low base.
Essential Eight can often be implemented faster, but it still demands solid engineering work: patching, configuration hardening, identity management, logging, and backup practices that actually work in real environments.
Many Australian businesses start with Essential Eight uplift to reduce immediate cyber risk, then move into ISO 27001 once they are ready for a broader governance and certification journey.

Which framework suits your Australian business?
Start with your drivers
Ask yourself three simple questions:
1. What is pushing this conversation?
-
-
Large enterprise customers asking for ISO 27001 certification or similar? ISO 27001 will likely be the expectation.
-
Government or defence contracts referencing Essential Eight maturity levels? You will need to demonstrate alignment with those controls.
-
2. What are your regulatory obligations?
-
-
If you are APRA‑regulated, CPS 234 requires you to maintain appropriate information security capability and controls; ISO 27001 can be a good way to structure this, with Essential Eight used to evidence specific technical measures.
-
All Australian organisations are subject to the Privacy Act, so you need to show that personal information is protected with reasonable security safeguards; both frameworks help, but ISO 27001 gives you a governance and risk lens as well.
-
3. What is your budget and internal capacity?
-
-
A full ISO 27001 certification project is more investment, but builds a repeatable management system that survives staff changes and board cycles.
-
Essential Eight uplift can be scoped and delivered in stages, aligned to your current maturity and risk appetite.
-
If you are not sure where you stand today, a structured gap assessment against both ISO 27001 and Essential Eight is often the most efficient way to get clarity. Siege Cyber runs these for organisations across Australia and can prioritise a roadmap that fits your budget rather than a theoretical ideal.
If you are not sure where your organisation sits on either framework, a gap analysis is a practical starting point. Siege Cyber offers ISO 27001 and Essential Eight gap assessments as standalone services so you get a clear, prioritised action plan before committing to a full project.
Can you use ISO 27001 and Essential Eight together?
You do not have to choose one or the other. In practice, the strongest outcome for many Australian businesses is:
-
Use ISO 27001 as the management system and governance layer.
-
Use Essential Eight as part of your technical control set and metrics within that system.
Several Australian commentators describe ISO 27001 as the framework that keeps Essential Eight funded, measured and maintained over time. Essential Eight delivers quick, visible uplift; ISO 27001 keeps it from sliding backwards.
At Siege Cyber, we regularly help clients integrate Essential Eight maturity targets into their ISO 27001 risk treatment plans and Statement of Applicability, so you get one coherent security story rather than two separate checklists.
If you are already using a compliance automation platform like Vanta or Drata to chase ISO 27001, Siege Cyber can act as your partner to tune the platform, interpret the gaps it finds, and ensure your Essential Eight‑style controls are actually effective in practice, not just ticking boxes.

How Siege Cyber can help
Siege Cyber is a Brisbane‑based cyber security firm that works with organisations across Australia on ISO 27001, Essential Eight and broader security uplift. Our ISO 27001 services cover everything from initial scoping and risk assessment through to implementation, internal audit support, and getting you ready for certification audits, whether you are starting from scratch or levelling up an existing ISMS.
We also run Essential Eight assessments and uplift projects using the latest ACSC maturity model, so you can see where you stand today and what it would take to reach a target maturity level that aligns with your risk and contractual obligations.
If you prefer a transparent view of costs before you start, Siege Cyber publishes standardised pricing for core compliance services on the website so you can budget with fewer surprises. Review our ISO 27001 service offering and compliance pricing to get a sense of timelines and typical project scopes.
If you are ready to compare ISO 27001 vs Essential Eight for your organisation, the next step is to visit siegecyber.com.au, review the ISO 27001 and Essential Eight service pages and compliance pricing, then get in touch with the team via [email protected] to schedule a short, no‑obligation discussion about your options. We can help you decide whether to pursue ISO 27001, Essential Eight, or a combined approach that makes sense for your risks, budget and growth plans.