ISO 27001 Gap Analysis: Finding Out Where You Stand Before Certification
If you’re thinking about ISO 27001 certification, a proper ISO 27001 gap analysis is the easiest way to find out where you stand before you spend serious time and money. It shows you how close you are to the standard today, which gaps matter most, and what needs to happen so you can face the audit with confidence.
A structured gap assessment also helps reduce ISO 27001 audit findings, because you have already identified and fixed the obvious issues before an external auditor walks in. In this article, I will walk through what an ISO 27001 gap analysis involves, how long it usually takes, and where it fits into your broader certification plan in Australia.

What is an ISO 27001 gap analysis?
An ISO 27001 gap analysis compares your current information security practices against the requirements of ISO 27001 and its Annex A controls. That includes looking at both your management system (governance, risk management, policies, processes) and the technical controls that support them.
In practical terms, a consultant will review your documentation, talk to key people and map what you are doing today against what ISO 27001 expects to see. The output is usually a structured report and remediation roadmap that tells you where you are compliant, where you are partially meeting the requirement, and where you have a clear gap.
For Australian organisations, the same assessment can also be used to line up ISO 27001 with the Privacy Act 1988, APRA CPS 234, and the ASD Essential Eight, so you are not building separate, conflicting frameworks. This is particularly helpful if you handle personal information, operate in financial services, or sell into government.
Why do a gap analysis before ISO 27001 certification?
You can go straight into implementation without a formal ISO 27001 gap analysis, but it usually means more rework and more surprises at audit. A good gap assessment gives you three things up front.
-
A realistic view of effort
-
A prioritised remediation plan
-
Fewer audit findings later
First, it gives you a realistic view of effort and cost. You will see how your existing security practices stack up and whether you are looking at a few months of focused work or a longer transformation.
Second, you get a prioritised remediation plan instead of a vague “tighten security” message from the board. A proper report will separate must‑do items for audit from nice‑to‑have improvements, so you can make sensible decisions about time and budget.
Third, identifying ISO 27001 gaps before audit reduces the number and severity of non‑conformities an auditor will raise, which saves time, money, and stress at the back end. Certification bodies report that most failed or delayed certifications come down to missing risk assessments, weak documentation, and poorly implemented controls, all of which can be picked up in a gap analysis.
If you want a deeper sense of the overall journey, Siege Cyber’s ISO 27001 consulting page sets out what the full project from scoping through to audit support usually looks like for Australian SaaS and technology companies.
What does an ISO 27001 gap analysis cover?
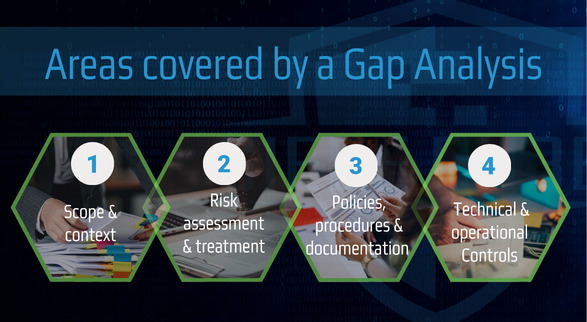
Every consultant has their own style, but a solid ISO 27001 framework gap analysis will typically cover several areas.
1. Scope and context
ISO 27001 expects you to define what parts of your organisation are in scope for certification, not just “the whole company”. In a gap analysis, we look at your products, locations, systems, and third parties, and test whether your proposed scope makes sense for your commercial goals and risk profile.
For example, many Australian SaaS companies only certify the platform and supporting functions that handle customer data, not every internal system from day one. Getting this right early avoids nasty surprises at audit when the certification body questions your boundaries.
2. Risk assessment and treatment
ISO 27001 is a risk‑based standard, and AS ISO/IEC 27001:2022 makes a formal risk assessment mandatory. During the gap analysis, we review how you currently identify, assess, and treat information security risks.
Common gaps include informal risk discussions with no written methodology, no clear risk appetite, and no link between identified risks and the Annex A controls you have chosen. These issues are fixable, but they will generate non‑conformities if you only discover them at Stage 2 audit.
3. Policies, procedures and documentation
Most organisations already have some security policies, but they are often incomplete, outdated, or not aligned with ISO 27001 language. In the gap analysis, we assess whether you have the core documents an auditor will expect to see, including:
-
Information security policy
-
Risk assessment and treatment methodology
-
Statement of Applicability
-
Incident management, access control, asset management, and supplier management procedures
We are not judging writing style; we are checking whether what is written matches what actually happens and whether it aligns with the standard. Auditors in Australia are increasingly wary of copy‑paste templates that do not reflect reality.
4. Annex A controls and technical measures
We then look at your existing technical and operational controls and map them against Annex A of ISO 27001:2022. This includes areas such as identity and access management, logging and monitoring, backup, vulnerability management, and secure development practices.
For many clients, this is where penetration testing, Essential Eight assessments, and broader security reviews they have already done become useful evidence, because they show that controls are in place and tested. We make sure you are getting credit for the work you already do instead of reinventing the wheel.

How long does an ISO 27001 gap analysis take?
“How long does an ISO 27001 gap analysis take?” is one of the first questions we get asked. The honest answer is that it depends on your size, complexity, and how prepared you are, but there are some typical ranges.
For a small to mid‑sized Australian SaaS or technology company, a focused gap analysis often takes between one and three weeks end‑to‑end. That covers workshops, document review, follow‑up questions and delivery of the report and remediation roadmap. Larger, highly regulated organisations can take longer, especially if multiple business units and stakeholders are involved.
At Siege Cyber, we typically structure an ISO 27001 gap analysis as a short engagement at the front of a broader certification project. Our ISO 27001 consulting service describes a staged approach where scoping and gap analysis are completed in the first couple of weeks, followed by risk assessment, implementation, and audit preparation over the next few months.
If you are not sure where your organisation stands, an independent gap analysis is a straightforward starting point. Siege Cyber offers ISO 27001 framework gap analyses as a standalone service or as part of our fixed‑price compliance packages, so you can choose the level of support that fits your situation.
How a gap analysis helps reduce ISO 27001 audit findings
No one enjoys long lists of audit findings. A good ISO 27001 gap analysis is designed to reduce audit findings by addressing issues before the certification body arrives.
First, it highlights missing or weak artefacts that auditors consistently look for, such as a formal Statement of Applicability, evidence of management review, and records of internal audits. These are common sources of non‑conformities in ISO 27001 audits worldwide.
Second, it identifies areas where you might be over‑promising in documentation compared to what actually happens. For example, if your policy says all high‑risk vulnerabilities are remediated within seven days but your tracking shows longer timelines, an auditor will pick that up quickly. Fixing these inconsistencies in advance avoids awkward conversations.
Third, by tying your existing practices to Annex A controls and your risk assessment, you can present a coherent story about why you made certain decisions, which auditors appreciate. In our experience, clients who invest in a proper pre‑certification gap analysis face fewer surprises and move through Stage 1 and Stage 2 audits faster.
Where pricing and automation platforms fit in
Budget is always a factor. Siege Cyber’s compliance pricing page outlines fixed monthly packages that include ISO 27001 support, internal audit, risk assessment, and penetration testing, with a typical journey from “start” to “audit‑ready” in 3–9 months. This can be more predictable than one‑off, time‑and‑materials projects, especially for growing teams that need ongoing support rather than a single engagement.
If you are already using Vanta or Drata, an ISO 27001 gap analysis is still valuable. Those platforms automate evidence collection and control monitoring, but they do not decide your scope, define your risk methodology, or explain Australian regulatory expectations to your board. Siege Cyber is an official partner of both Vanta and Drata, so we can run the gap analysis directly within your existing environment and then help you close the gaps that automation cannot handle on its own.
You can see how the gap analysis, broader consulting support, and pricing work together on the Siege Cyber ISO 27001 consulting and compliance packages pages.
What happens after the ISO 27001 gap analysis?
The gap analysis is not the end goal; it is the starting point. Once you have your findings and remediation roadmap, you can decide how you want to move forward.
Some organisations have strong internal capability and use the report as a blueprint for their own implementation. Others prefer a guided approach where a consultant stays involved through policy development, control implementation, internal audit and audit support.
At Siege Cyber, the common next steps after a gap analysis include:
-
Running a proper ISO 27001‑aligned risk assessment
-
Developing or updating policies and procedures
-
Implementing or tightening key technical and operational controls
-
Conducting an internal audit and management review before certification
If you want a partner to stay with you from gap analysis through to passing the audit, our ISO 27001 consulting service and rapid compliance packages are designed with exactly that in mind.
Ready to find out where you stand?
If ISO 27001 is on your radar, an ISO 27001 gap analysis will tell you where you stand today and what it will realistically take to reach certification. You will end up with a clear list of gaps, a prioritised remediation plan, and a far lower risk of painful audit findings later.
Siege Cyber helps Australian businesses get ISO 27001‑ready without turning their operations upside down. Our team has guided numerous organisations through ISO 27001 certification, and every one has passed their audit.
If you would like an honest assessment of your current position, visit siegecyber.com.au, explore our ISO 27001 consulting services, or contact us to book a free initial consultation. We will talk through your goals, timelines, and constraints, and recommend a right‑sized approach so you know exactly what comes next.