5 Types of Penetration Testing Every Australian Business Should Know
A lot of business owners hear the words “penetration testing” and assume it refers to one specific thing. It does not. There are several distinct types of penetration testing, and choosing the wrong one means you spend money testing the wrong part of your environment while real vulnerabilities go undetected. This guide explains what penetration testing actually involves, breaks down the five most common types, and helps you work out which one your business needs and how often you should be doing it.
What Is Penetration Testing?
A penetration test, or pen test, is an authorised, simulated cyberattack carried out by a security professional. The tester uses the same tools and techniques a real attacker would use, attempts to exploit vulnerabilities in your systems, and then documents exactly what they found and how they got in.
The key word is “authorised”. Everything is agreed in writing before testing begins. You know it is happening. What you do not know is what the tester is going to find, and that is the point.
What penetration testing is not is a vulnerability scan. A vulnerability scan uses automated tools to flag known weaknesses in your systems. It is faster and cheaper, but it does not tell you whether those weaknesses can actually be exploited, how far an attacker could get, or what the real-world business impact would be. A proper pen test involves a skilled human making judgement calls, chaining vulnerabilities together, and thinking the way an attacker thinks.
The 5 Core Types of Penetration Testing
1. External Network Penetration Testing
This is probably the most common test businesses commission. An external network pen test looks at your internet-facing systems, which includes your firewall, VPN gateways, remote access points, and any other services exposed to the public internet.
The tester approaches your environment from the outside, exactly as a remote attacker would, and tries to find a way in. If they succeed, they document how far they were able to get and what they could have accessed. Most businesses are surprised by what their external footprint actually looks like once someone maps it properly.
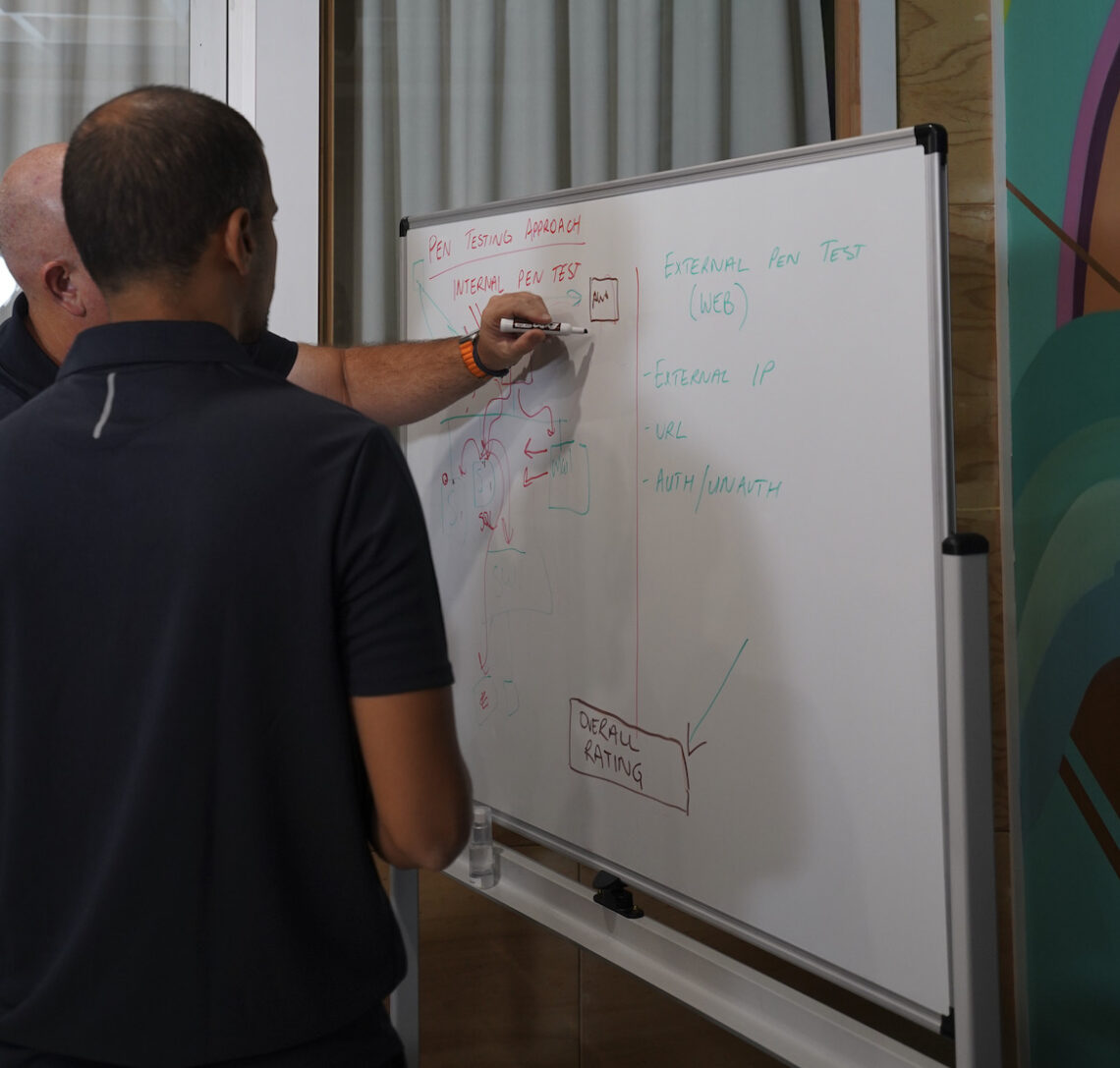
2. Internal Network Penetration Testing
An internal network pen test simulates an attacker who is already inside your network. This might be a malicious insider, a contractor with legitimate access, or someone who has managed to get a foothold through a phishing attack or compromised credentials.
This type of test tends to expose weaknesses in network segmentation, lateral movement pathways, and privilege escalation opportunities. It answers a question that many businesses overlook: if someone gets past your perimeter, how far can they actually go? In most environments, the answer is further than expected.
3. Web Application Penetration Testing
If your business runs a customer portal, an online platform, a SaaS product, or any web-based application, a web application pen test should be on your radar. This test follows the OWASP testing methodology and looks for vulnerabilities specific to web applications, including injection flaws, broken authentication, insecure data exposure, and logic errors that automated scanning tools routinely miss.
Web application testing is frequently required for SOC 2 and ISO 27001 audits, particularly when your application handles customer data. It is also highly relevant for businesses subject to the Australian Privacy Act 1988, where demonstrating reasonable security measures around personal data is a legal obligation.
4. API Penetration Testing
APIs, the connections that allow different software systems to talk to each other, have become one of the most common attack surfaces in modern environments. Yet they are frequently excluded from web application tests or only tested superficially.
A dedicated API pen test examines your endpoints for authentication weaknesses, excessive data exposure, broken object-level authorisation, and other issues catalogued in the OWASP API Security Top 10. If your product relies heavily on API integrations or you expose APIs to third parties, this test is worth including in your security programme.
5. Cloud Penetration Testing
Moving infrastructure to AWS, Azure, or Google Cloud does not make it secure by default. Cloud environments introduce a different set of risks, including misconfigured storage buckets, overpermissioned service accounts, insecure identity and access management, and poorly secured serverless functions.
A cloud pen test reviews your specific cloud environment for these issues, working within the cloud provider’s acceptable use policies. It is a different discipline from traditional network testing and requires testers who understand cloud architecture and how it is commonly misconfigured in practice.
Not sure which type of test is right for your environment? Siege Cyber offers a free initial consultation to help you scope the right engagement. We will ask the right questions, tell you honestly what we recommend, and give you a clear picture of what it involves before you commit to anything. Start the conversation here.
How Often Should You Do Penetration Testing?
This is one of the most practical questions businesses ask, and the answer is grounded in both risk and regulatory expectation.
For most Australian organisations, annual penetration testing is the baseline. The following frameworks provide more specific guidance:
-
APRA CPS 234 requires APRA-regulated financial entities to test at least annually and after significant system changes
-
ISO 27001 expects regular testing intervals, with annually being the common practice
-
ASD Essential Eight does not prescribe a specific frequency, but expects testing that is proportionate to your maturity level and risk profile
-
SOC 2 does not mandate a frequency, but auditors expect evidence of testing during the audit period, particularly for a Type II report
Beyond regulatory requirements, there are practical triggers that should prompt an additional test regardless of when you last did one:
-
After a major system change or new application deployment
-
Before a significant contract, tender submission, or due diligence process
-
After a security incident that suggests your environment was probed or compromised
-
When you add new internet-facing services or change your cloud architecture
Annual testing keeps you reasonably covered. Risk-based testing keeps you actually covered.
Black Box, Grey Box, and White Box: What Is the Difference?
These terms describe how much information the tester is given about your environment before they start.
A black box test gives the tester no prior information. They start from scratch, the way a real external attacker would. It is realistic but can be slower and may miss issues that would only surface with more context.
A grey box test gives the tester some information, such as credentials for a standard user account or documentation about the application architecture. This is the most common approach and typically produces the most useful results within a fixed budget.
A white box test provides the tester with full information, including source code, architecture diagrams, and full access credentials. It is thorough and efficient, and is often used for web and API testing where understanding the application logic makes the tester significantly more effective.
For most Brisbane businesses commissioning their first pen test, grey box is the right starting point.
What Happens After the Test?
A pen test is only as useful as what you do with the results. A quality report includes an executive summary for business stakeholders, a technical findings section for your IT team, clear risk ratings for each finding, and prioritised remediation recommendations.
Once you have addressed the findings, a retest confirms that vulnerabilities have actually been resolved, not just noted and forgotten. Make sure a retest is included in your quote before you engage a provider.
Talk to a Brisbane Pen Testing Team That Explains Things Clearly
Siege Cyber provides penetration testing services across all five test types, with transparent pricing and plain-English reporting that your whole team can act on. Whether you are testing for the first time, working toward ISO 27001 or SOC 2, or simply want to know where your real risks are, we can help.
Visit siegecyber.com.au/services/penetration-testing/ to learn more about how we approach testing, or view our pen test pricing to understand what a properly scoped engagement costs.
Siege Cyber has been helping businesses across Australia with penetration testing, compliance, and cyber risk for over 20 years. If you’d like to discuss what type of testing makes sense for your organisation, or if you’re preparing for an ISO 27001 or SOC 2 audit and need testing as part of that process, get in touch.
You can reach us at siegecyber.com.au or email [email protected] directly. We’re based in Brisbane but work with clients across the country.